Latest Trends
Get the latest in Tech,
once a week. Free.

VR/AR
Security
5 Tips To Avoid Potential Dangers Of CookiesApril 2, 2025Security / System PerformanceUsually, in the Internet, user details like (searches, login data etc.) are stored as cookies. They are responsible for the personalized browsing experience, and it’s the reason why we see advertising related to our browsing history. i.e cookies represent a saving of energy and time for users.
Despite being an absolutely common element, they are just little snippets of text and/or data that is transferred between the web server and browser each time you open a session. That being, they can also become a real problem for security if we do not take the proper precautions.
The first thing to know is that there are two main types of cookies, temporary and permanent. The first, also known as ‘session’, only last for the duration of the session.
Top 10 Ways To Protect Yourself From Cyber Crime & Hacks
How to Control Cyber Crime. Cyber crime refers to any criminal activity that takes place over the Internet. Examples include fraud, malware such as viruses
Read More
Once the browser is closed they disappear. Instead, permanent cookies exist for a variable number of sessions or until manually eliminated. Many web applications use these cookies for finding the geo-location of the user automatically.
They are also other cookies, so-called ‘ third ‘, which are present in certain web servers in order to track the online behavior of users for commercial or advertising purposes.
This is how we see ads related products to our interests. According to this description, cookies facilitate and simplify many processes in web browsing.
But there are also many critical voices against them, and against the use that is given to personal information that they collect. In some extreme cases, there have been attacks on computers of users who unknowingly shared their cookies.
That is why we came up with 5 simple tips to protect you from dangers of cookies:
1. Clean or delete cookies:
Nothing is as simple as deleting browsing history and cookies at the end of the session and staying safe. However, if we are forgetful or lazy, there are software that can do this work for you. Like PURE 3.0.
2. Modify browser settings:
So you have control over the information that tracks cookies. Go to privacy settings and configure your browser options. For example, Firefox and Safari offer greater control over that information.
3. Use Add-Ons:
Using this tool you can manage browser cookies more specifically and even enable only those with whom we want to share our online information.
Erase All Your Private and Sensitive Data In A Click
We will show you an application that will help you protect your privacy by easily removing all your private and sensitive data from PC with just a click on
Read More
4. Share with moderation:
Like almost everything that happens on the Internet and in everyday life, common sense is our best ally. Thus, it is advisable not to enter personal data in places where cookies can store and always remember not leave open any account or session.
5. Protect:
The best way to protect your online privacy is to have a good security solution ( AntiVirus ) installed. Anyhow even with the most advanced antivirus installed on your computer, you may still be a victim of these attacks.
Your Thoughts
Have you tried these measures before? If so, were you successful in keeping threats due to cookies away? Share with us in the form of comments below. Also, don’t forget to share this article with your friends and stay protected from any potential threats. [...]
Erase All Your Private and Sensitive Data In A ClickMarch 30, 2025PC Hacks / SecurityIn OnlineCmag we have spoken more than once of issues related to privacy and have also discussed different methods to protect your identity and trail anywhere on the Internet.
Throughout the entire span we’ve been here we have explained several key tricks, like How to delete all traces of your activity on a click and starting the incognito mode of Google Chrome default but that’s not all, in the Windows section you will find dozens of such useful tips.
Today we will show you another such application that will help you protect your privacy by easily removing all your private and sensitive data.
In this case, the application is the ‘Free Privacy Eraser 3.5′ and its function is to delete private data for free, as its name suggests.
Free Privacy Eraser 3.5 works in a very simple way, you just have to select the areas you want to review, press the start button and once finished press the clear button.
By this application we can eliminate many issues related to privacy, including the following:
Windows
History of opened documents
Search history
Temporary Files
Microsoft Office trace
Paint trace
Messaging Application
logs and cache different places
Etc.
Web browsers (Internet Explorer / Netscape / Firefox / Opera / Google Chrome)
Cache
Cookies
Record
Downloads
AutoComplete
Passwords
Etc.
Furthermore, the application offers the following features added:
1. Support for accessories: Amenities including over 100 accessories for popular applications such as WinRAR, WinZip, Adobe, PowerDVD, etc.
2. Custom Options: You can save cookies, make a secure erase, etc.
Certainly, Free Privacy Eraser 3.5 is one of the simplest and most complete applications that can be found at zero cost, so we recommend its use so that you can be a bit more secure than you are now.
Cleanersoft | Free Privacy Eraser 3.5 [...]
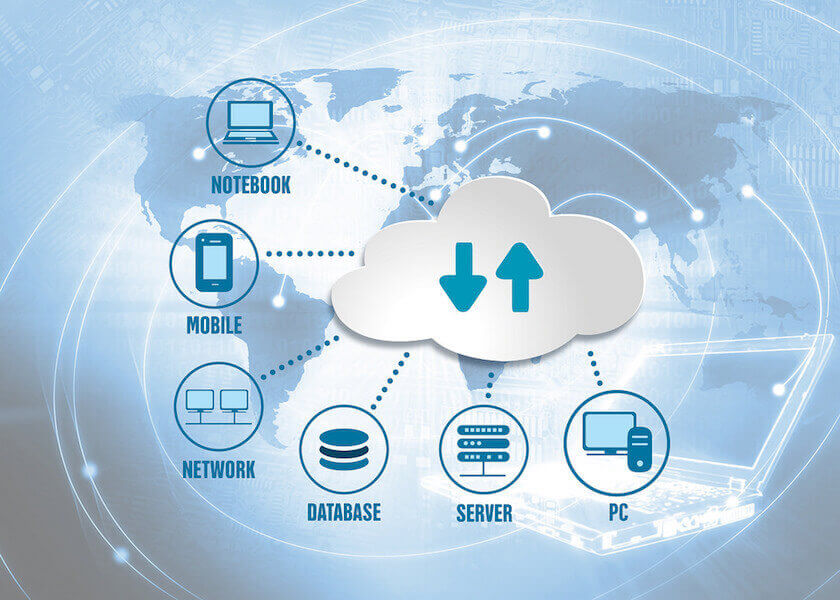
The Ultimate Cloud Data Security Mantras For Individuals and BusinessesMarch 27, 2025SecurityCan you guarantee the data you have stored on the cloud is safe? It could be a little harsh to state it this way but the point is, you can’t. Yes, this is the fact that’s actually muddling everyone from CEOs of most reputed organizations to those of small businesses and every individual storing private data on the cloud.
Don’t worry, its not really even that bad though with security teams of cloud service providers burning the candle on both ends in keeping away the attackers from your data. However, there are many protective measures you can take on your part to ensure maximum integrity and security of your data on the cloud. In this article we mention a few very important steps, we suggest you to implement at the earliest.
(If at all you are new to the entire cloud thing, here’s what you should check out first – click here)
Here are 5 Mantras on Cloud Data Security for you:
Passwords – Be More Than Careful
You must have come across this warning many a times in your daily routine. But the fact is, people don’t really learn from others mistakes. If it were the case, the stats that 90% of all the passwords can be cracked within seconds would have just been a myth. But unfortunately it’s the truth. Until and unless you create strong passwords, almost everything you put on the internet can be compromised in no time. So make sure you follow these fundamental rules while setting up passwords anywhere on the internet:
Use a strong and difficult to guess password.
Never share your passwords with strangers, and to some point even with peers.
Also set up different passwords to different accounts.
Prefer using a standard password manager, and for lot more about them, click here.
Sensitive Information – Opt storing elsewhere
This might sound crazy, but considering the safety first rule, use the virtual world for data storage as less as possible. There’s actually no other alternative to storing your data on the internet and praying for no evil eyes to target it. However the best suggestion, if you are an individual would be to store less sensitive information on the cloud and opt for other means.
In case you are a company, you could go for the hybrid cloud model and deploy other tools like, say, honeypot etc.
Encrypted Cloud Storage – For Businesses
If you are ready to invest big on cloud data security, then this option is always available for you. These encrypted cloud storage services in addition to storage and backup, also provides facilities like encryption and decryption of all the data in your local machine. This is termed as the ‘zero-knowledge’ privacy, and is the highest level of cloud security in the market.
Under this condition, no one except you, not even the personals running the cloud (service providers) can access your information. To name a few, Spideroak, Dropbox, Box are all such service providers. But the most important part lies in identifying the potency of data at hand and deciding whether or not to invest big for its security.
B1 Free Archiver – The low budget encryption
Not every business can invest that big in reaching out for encrypted cloud services, but there are a lot of other alternatives as well. B1 Free Archiver, for example does a really good job. Likewise, there are a lot of tools over there in the internet which can encrypt all your data and protect it with a password.
The additional benefit especially with B1 Free Archiver is that once encrypted, the entire data is converted into the B1 file format and any computer on which this data is being accessed needs to have B1 Free Archiver installed on it and this tool (archiver) is believed to be more safer and effective than the zip files.
Cloud Data Security – Knowledge Matters!
Believe it or not, without knowing what you are doing, just deploying a cloud model will only get you into trouble. The best way to be prepared to any of the bizarre consequences is to have complete knowledge on the cloud model (public, private or hybrid) you require, the terms of the cloud service provider and lots of analysis to maintain the perfect balance between protection and time/money.
Other than all these, with the sensitivity of data stored, physical security denying unauthorized access into the data center is also mostly suggested. Call it preparing for bad times, in addition to the above mentioned mantras make sure you read the terms and conditions of the cloud service provider carefully, believe me you don’t want to hand your most valuable data into the hands of someone playing fool with you.
[...]
Web Guides
Join Our Tech Community For Free
How To
5 Tips To Avoid Potential Dangers Of CookiesApril 2, 2025Security / System PerformanceUsually, in the Internet, user details like (searches, login data etc.) are stored as cookies. They are responsible for the personalized browsing experience, and it’s the reason why we see advertising related to our browsing history. i.e cookies represent a saving of energy and time for users.
Despite being an absolutely common element, they are just little snippets of text and/or data that is transferred between the web server and browser each time you open a session. That being, they can also become a real problem for security if we do not take the proper precautions.
The first thing to know is that there are two main types of cookies, temporary and permanent. The first, also known as ‘session’, only last for the duration of the session.
Top 10 Ways To Protect Yourself From Cyber Crime & Hacks
How to Control Cyber Crime. Cyber crime refers to any criminal activity that takes place over the Internet. Examples include fraud, malware such as viruses
Read More
Once the browser is closed they disappear. Instead, permanent cookies exist for a variable number of sessions or until manually eliminated. Many web applications use these cookies for finding the geo-location of the user automatically.
They are also other cookies, so-called ‘ third ‘, which are present in certain web servers in order to track the online behavior of users for commercial or advertising purposes.
This is how we see ads related products to our interests. According to this description, cookies facilitate and simplify many processes in web browsing.
But there are also many critical voices against them, and against the use that is given to personal information that they collect. In some extreme cases, there have been attacks on computers of users who unknowingly shared their cookies.
That is why we came up with 5 simple tips to protect you from dangers of cookies:
1. Clean or delete cookies:
Nothing is as simple as deleting browsing history and cookies at the end of the session and staying safe. However, if we are forgetful or lazy, there are software that can do this work for you. Like PURE 3.0.
2. Modify browser settings:
So you have control over the information that tracks cookies. Go to privacy settings and configure your browser options. For example, Firefox and Safari offer greater control over that information.
3. Use Add-Ons:
Using this tool you can manage browser cookies more specifically and even enable only those with whom we want to share our online information.
Erase All Your Private and Sensitive Data In A Click
We will show you an application that will help you protect your privacy by easily removing all your private and sensitive data from PC with just a click on
Read More
4. Share with moderation:
Like almost everything that happens on the Internet and in everyday life, common sense is our best ally. Thus, it is advisable not to enter personal data in places where cookies can store and always remember not leave open any account or session.
5. Protect:
The best way to protect your online privacy is to have a good security solution ( AntiVirus ) installed. Anyhow even with the most advanced antivirus installed on your computer, you may still be a victim of these attacks.
Your Thoughts
Have you tried these measures before? If so, were you successful in keeping threats due to cookies away? Share with us in the form of comments below. Also, don’t forget to share this article with your friends and stay protected from any potential threats. [...]
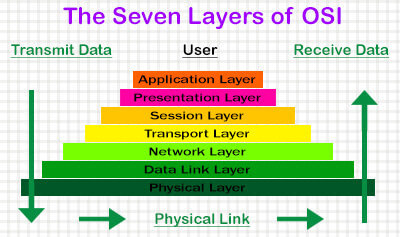
How To Use The Same Mouse And Keyboard For Multiple ComputersMarch 31, 2025PC Hacks / Web GuidesIf our work demands us to use two or more computers at the same time, alternating between the two is quite tedious and unproductive. But with Synergy 1.3.1 . We can configure them with a single mouse and keyboard, we will be able to control the same way in which we handle a single computer and two monitors extending the desktop. Simply dragging the pointer to the side of the screen jumps to the another computer.
In addition, the major amenities provided include the ability to share the clipboard, to copy and paste text and images between computers.
You can connect systems with different operating systems ( Windows, Linux and Mac ), however, the essential criteria to use Synergy is that computers must be networked.
Steps To Use The Same Mouse And Keyboard For Multiple Computers In A Network :
Step 1 : Choose the server :
We must choose a computer to convert it to a server, this will be the main component where the clients keyboard and mouse are connected. As a general rule, we will choose the one we use most frequently.
If you have activated the Windows Firewall , you must add an exception for Synergy in order to receive incoming connections, to do so, go to Control Panel / Windows Firewall , once here, inside the tab Exceptions , select Add Program and add Synergy to your list. If you use another firewall program, you must also make sure of the appropriate adjustments.
After installing Synergy on your server, execute it, and in the first screen, mark the option Share this computer’s keyboard and mouse (server) , and click the button config , because all configuration parameters are set on the server.
Step 2 : Add your screens :
The first configuration step is to add all the computers we want. On this sense, we must know the name of each computer, if you do not know, you can consult or change in Control Panel / System , the tab name equipment.
Once you have taken note of the names, just press the + key to display a screen ” Enter The Name Of The First Computer “. Then click on OK . Repeat this process for all computers you wish to add.
It is important to note at the time of the connection, if you notice some strange behavior with keys Caps Lock , Num Lock and Scroll Lock , we return to these options and check the appropriate boxes to enable bidirectional communication.
Step 3 : Create links:
After completing the process of adding the systems, it’s time to create focal points to jump from one screen to another. The most common configuration is to have two devices side by side, so that rising from the right of the left-most, enter the second and vice versa. However, we can place more than two and configure the way that suits us.
At the bottom menu that we saw in the previous step, in the first dropdown, choose the name of the screen to the right and select left side go to our left monitor. Percentages also see where we can adjust the sizes of the linked areas. After adjusting the parameters, just press + .
As expected, we perform the same action but contrary to our other display and thus able to move the mouse in both directions. Once configuration is complete, proceed to save it by clicking OK and returning to the main screen. We are ready to start our server, so you will press Start and Synergy will minimize to the system tray being pending connections.
Step 4 : Connect customers :
With our server running it’s time to connect the clients. Now Install and run this application in the computer you want to connect. Now on the main screen, select the option Use another computer’s shared keyboard and mouse (client) , write down the name of the server and press the button Start .
If everything went correctly, Synergy will be minimized and you can see its icon in the system tray with a yellow beam. From this moment, we can move the mouse connected to the server to see how it moves from one screen to another. In the event that has not been able to connect a console indicating the error appears and you must therefore review the configuration and verify that the equipment is properly connected to the local network.
Step 5 : Set and forget :
Since we will only use a keyboard and mouse, we are concerned that whenever computers are turned ON, they are automatically connected together without having to launch Synergy in each of them. On the Home screen, press the button autostart , now a dialogue with lots of text, but only two buttons will be displayed, the first install this feature for the current user and the right will do the same with all users of the computer.
Hardware or software?
We face an interesting case because using a program we can emulate the same work as would a physical device: A KVM switch (Acronym for Keyboard Video Mouse ), a device that allows us to control multiple computers using a single keyboard, monitor and mouse. These devices are connected to the corresponding ports on the CPU and allow us to switch between them by a switch without changing the peripheral hand.
Therefore, we could consider a virtual KVM Synergy, which offers some improvements such as: share clipboard, create the illusion of working with a single desk and the not inconsiderable advantage of saving a bunch of cables. However, you can use a physical KVM, if we want to use one screen to control multiple PCs or if they are not on the same network. [...]
Erase All Your Private and Sensitive Data In A ClickMarch 30, 2025PC Hacks / SecurityIn OnlineCmag we have spoken more than once of issues related to privacy and have also discussed different methods to protect your identity and trail anywhere on the Internet.
Throughout the entire span we’ve been here we have explained several key tricks, like How to delete all traces of your activity on a click and starting the incognito mode of Google Chrome default but that’s not all, in the Windows section you will find dozens of such useful tips.
Today we will show you another such application that will help you protect your privacy by easily removing all your private and sensitive data.
In this case, the application is the ‘Free Privacy Eraser 3.5′ and its function is to delete private data for free, as its name suggests.
Free Privacy Eraser 3.5 works in a very simple way, you just have to select the areas you want to review, press the start button and once finished press the clear button.
By this application we can eliminate many issues related to privacy, including the following:
Windows
History of opened documents
Search history
Temporary Files
Microsoft Office trace
Paint trace
Messaging Application
logs and cache different places
Etc.
Web browsers (Internet Explorer / Netscape / Firefox / Opera / Google Chrome)
Cache
Cookies
Record
Downloads
AutoComplete
Passwords
Etc.
Furthermore, the application offers the following features added:
1. Support for accessories: Amenities including over 100 accessories for popular applications such as WinRAR, WinZip, Adobe, PowerDVD, etc.
2. Custom Options: You can save cookies, make a secure erase, etc.
Certainly, Free Privacy Eraser 3.5 is one of the simplest and most complete applications that can be found at zero cost, so we recommend its use so that you can be a bit more secure than you are now.
Cleanersoft | Free Privacy Eraser 3.5 [...]


![The Artificial Intelligent Personal Assistants [Future Tech]](https://onlinecmag.com/wp-content/uploads/2015/02/iphone_4s_showing_siri.jpg)